
Protecting businesses
that can’t afford to fail
When nothing happens, everything is working.
Real-time security across OT/IT, and physical environments.
See how we make nothing happen to protect critical operations.
Power keeps flowing. Production keeps moving. Pipelines keep running. That’s what nothing looks like. Because when nothing happens, everything works. No breaches. No ransomware. No downtime. Just business as usual.
The Omny Platform
See how our features fit together, each one built for industrial security.
From asset-level insights to executive-ready reports, everything is designed to support action.


Respond
Incident Response
Recover
Business Continuity
See every asset, connection, and activity across IT, OT, and physical security—that goes beyond network monitoring.
Read MoreConnect asset data, network flows, vulnerabilities, and compliance findings into reports that contextualize new threats and guide action.
Read MorePartnering with


Real threats don’t operate in silos
That’s why we designed a scalable, real-time, and field-tested platform that gives your teams the visibility they need. The only platform built for cyber-physical security with IT, OT, and physical security insights in one place.



Different users. Different views.
CISO gets one clear view of cyber risks and resilience across the entire business. Threats, vulnerabilities, and security controls are connected to the systems, so that priorities are set by business impact, not the number of alerts. Teams can work from the same status and actions, making governance and board reporting easier.
![CSO_CISO[63]](https://www.omnysecurity.com/hs-fs/hubfs/Module%20Images/CSO_CISO%5B63%5D.png?width=1895&height=1095&name=CSO_CISO%5B63%5D.png)
As a Security Risk Manager, be able to keep risk plans current without having to start from scratch. When threats change, you can quickly see which assets are impacted, what controls are in place, and what needs review. Reuse previous assessments, assign actions to owners, track progress, and stay audit-ready with less manual work.
![Sr Ops Manager[44]](https://www.omnysecurity.com/hs-fs/hubfs/Module%20Images/Sr%20Ops%20Manager%5B44%5D.png?width=1939&height=1139&name=Sr%20Ops%20Manager%5B44%5D.png)
SOC Analysts get the context they need as soon as an alert comes in. See what device is connected to the IP, which system is affected, and how critical it is to operations. Focus on what is important and reduce false alarms. Incidents and updates stay in one place, making it easier to hand over work and coordinate with operations.
![SOC analyst[99]](https://www.omnysecurity.com/hs-fs/hubfs/Module%20Images/SOC%20analyst%5B99%5D.png?width=1939&height=1139&name=SOC%20analyst%5B99%5D.png)
For OT/IT Operators, vulnerability work becomes far less manual. It compares CVE alerts to your OT/IT inventory, removes duplicates, and cleans up vendor and product names so you don’t chase the same issue across tools. You see what is affected and how urgent it is, making it easier to make patch decisions and track work orders.
![IT Eng[90]](https://www.omnysecurity.com/hs-fs/hubfs/Module%20Images/IT%20Eng%5B90%5D.png?width=1939&height=1139&name=IT%20Eng%5B90%5D.png)
Tailored industry solutions
Stay ahead of security threats before they disrupt operations.
A security breach—whether cyber or physical—can halt production, cut off energy supply, or put people at risk. Omny delivers real-time risk intelligence across IT, OT, and physical security, helping you detect vulnerabilities early and take action before they escalate.

Protect operations from digital and physical threats while maintaining safety and supply chain security.
Read More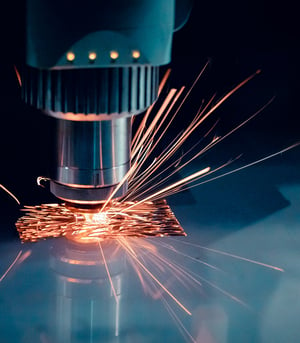
Manage security risks across IT, OT, and physical assets while keeping pace with digitalization and automation without disruption to operations.
Read More
Safeguard critical energy infrastructure from evolving cyber and physical threats.
Read MoreWhy choose between working smarter or faster?
Our clients see real improvements in both security and efficiency.
